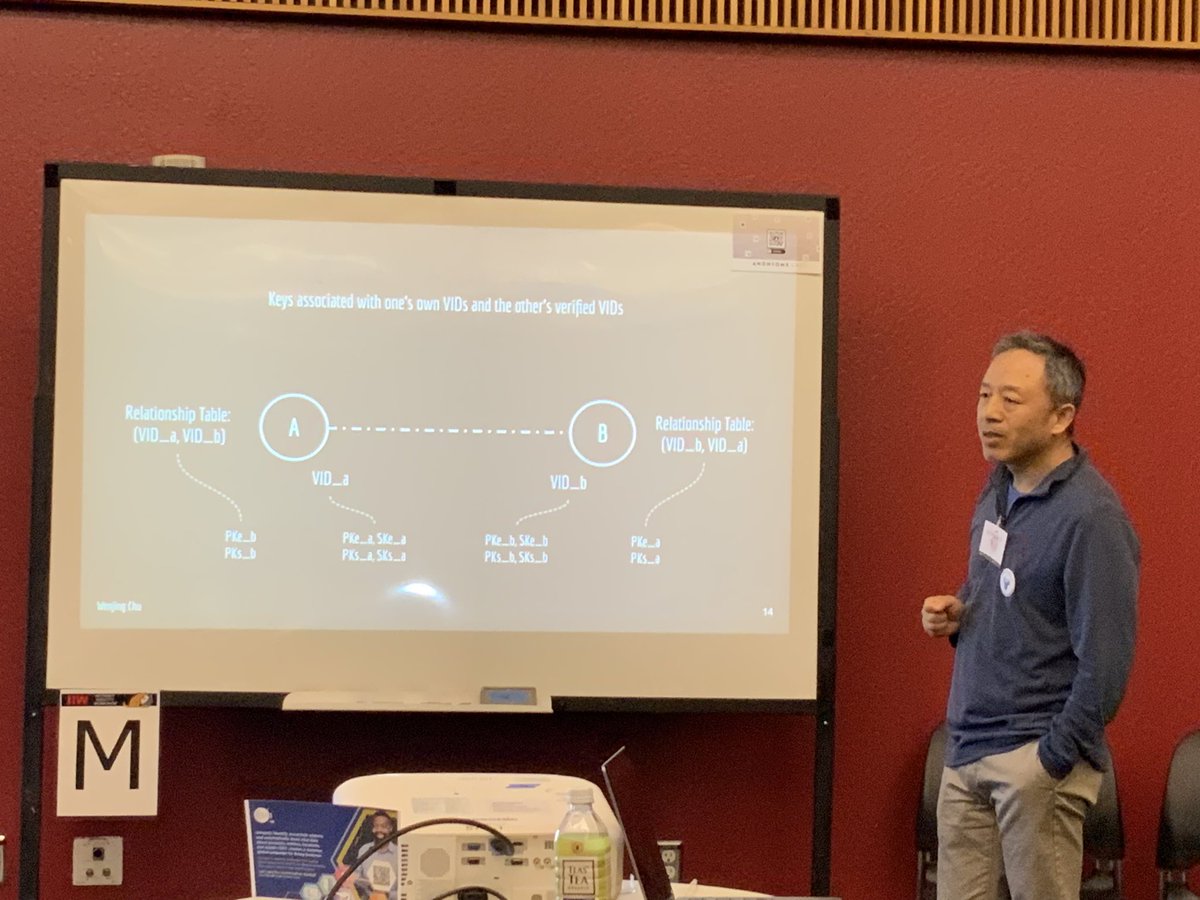
At #IIW 38, @wenjing covers how Alice and Bob use each other’s verifiable identifiers (VIDs)—which can be #DIDs—to discover & verify each other’s public #encryption and #signing keys in order to start sending messages over the #ToIP Trust Spanning Protocol trustoverip.org/blog/2024/04/1…
1
0
12
326
0
Download Image
@drummondreed @wenjing Alice and Bob need #zerotrust assurance of the quality, confidentiality, and strong binding of the other party's cryptographic keys. These are operational security requirements, not just protocols. We must remove reliance on human trust entirely. #UNS #UCA #themeshisthenewweb