Ethereal @ethereal__vx
art & malware *-* @vxunderground github.com/ethereal-vx Ring 0 Joined April 2019-
Tweets666
-
Followers2K
-
Following606
-
Likes6K
2 years dayum <3 keep falling in love a lil more each day. so so grateful to have gotten this opportunity and those who believed in me :3
2 years dayum <3 keep falling in love a lil more each day. so so grateful to have gotten this opportunity and those who believed in me :3
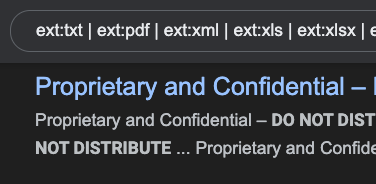
Google Dork - Sensitive Docs 📄 ext:txt | ext:pdf | ext:xml | ext:xls | ext:xlsx | ext:ppt | ext:pptx | ext:doc | ext:docx intext:“confidential” | intext:“Not for Public Release” | intext:”internal use only” | intext:“do not distribute” Discover internal files 👀
Did you know that LSASS has the ability to execute arbitrary kernel-mode addresses? I wrote a small proof of concept that allows administrators to execute unsigned code in the kernel if LSA Protection is disabled. github.com/floesen/KExecDD
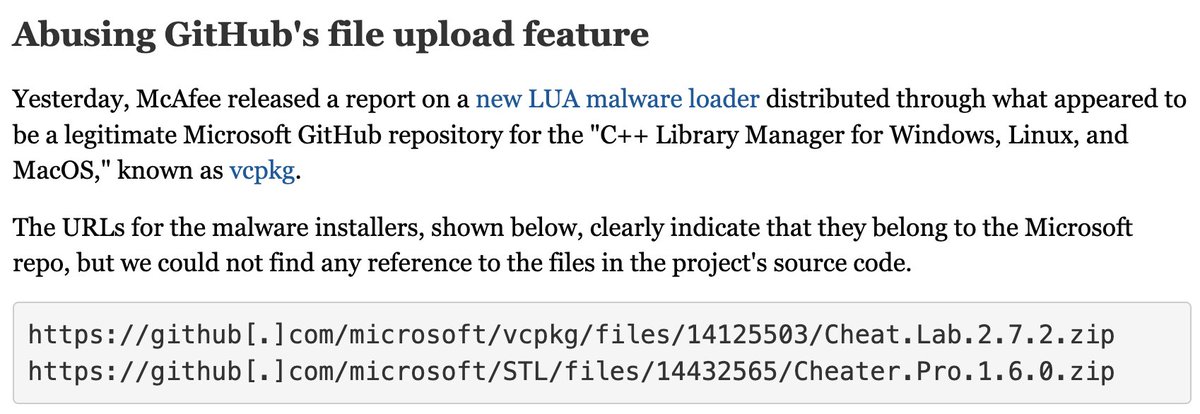
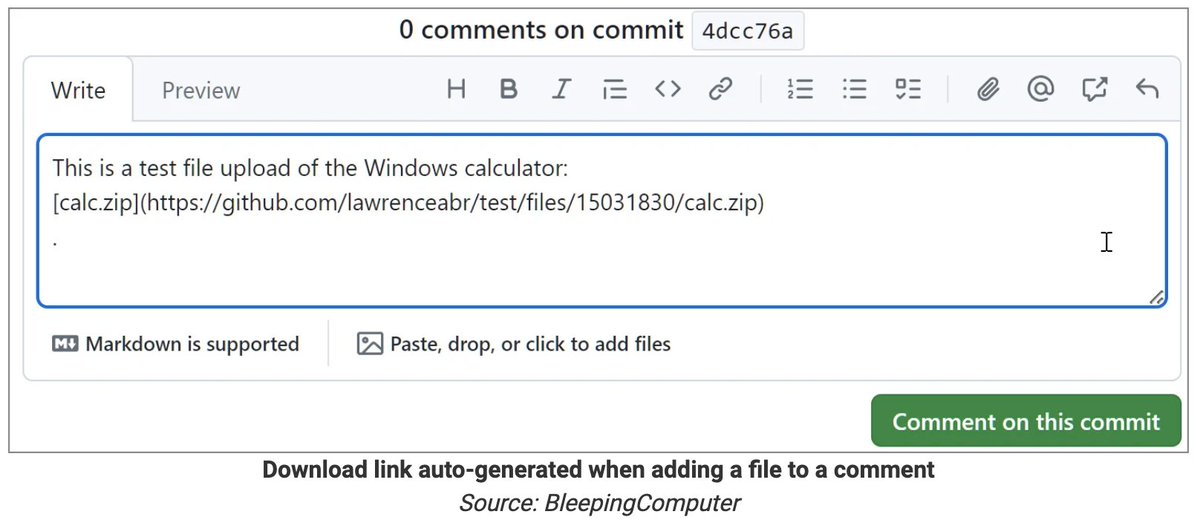
A GitHub flaw lets attackers upload executables that appear to be hosted on a company's official repo, such as Microsoft's—without the repo owner knowing anything about it. The following URLs, for example, make it seem like these ZIPs are present on Microsoft's source code repo:…
So @j00ru published two posts on Windows Registry; given that there were a lot of fixes in Windows Registry in recent months I expect these to be fun ;) googleprojectzero.blogspot.com/2024/04/the-wi… googleprojectzero.blogspot.com/2024/04/the-wi…
"From BYOVD to a 0-day: Unveiling Advanced Exploits in Cyber Recruiting Scams" published by Avast. #FudModule, #CVE-2024-21338, #KaolinRAT, #BYOVD, #CTI, #OSINT, #LAZARUS decoded.avast.io/luiginocamastr…
A first look at Android 14 forensics blog.digital-forensics.it/2024/01/a-firs…
I'm very excited to share my blogpost series (including PoC code) about a remote, interactionless iPhone exploit over iMessage: googleprojectzero.blogspot.com/2020/01/remote…
G DATA's Banu Ramakrishnan writes about a malicious Android app that masquerades as Google Chrome. The malware takes advantage of the popularity of and trust associated with Chrome to trick users into downloading and installing it. gdatasoftware.com/blog/2024/04/3…
I just discovered @artem_i_baranov blog and OMG?! If you're into windows kernel/internals it's an AMAZING goldmine 😯🤯 artemonsecurity.blogspot.com
always remember you're pretty cool and do pretty cool stuff <3
🔥🔥Announcement: Opening EXPMON for Everyone. justhaifei1.blogspot.com/2024/04/openin… EXPMON is a sophisticated exploit detection (and analytics) system specifically designed and built for detecting zero-day/unknown file-based exploits. pub.expmon.com
"Analysis of *.chm malware" published by Plainbit. #CHM, #CTI, #OSINT, #LAZARUS blog.plainbit.co.kr/chm-malware-an…
Tracking MatanBuchus Dropper Sites Through Hardcoded Certificate Values A short guide to leveraging subdomains, certificates, time filters and cert providers to hone in on malware hosting sites. embeeresearch.io/tls-certificat… #malware #threatintel
Uncovering Malicious Infrastructure With DNS Pivoting New blog experimenting with DNS and Domain pivoting to uncover malicious infrastructure🔥 embee-research.ghost.io/infrastructure… #malware #threatintel
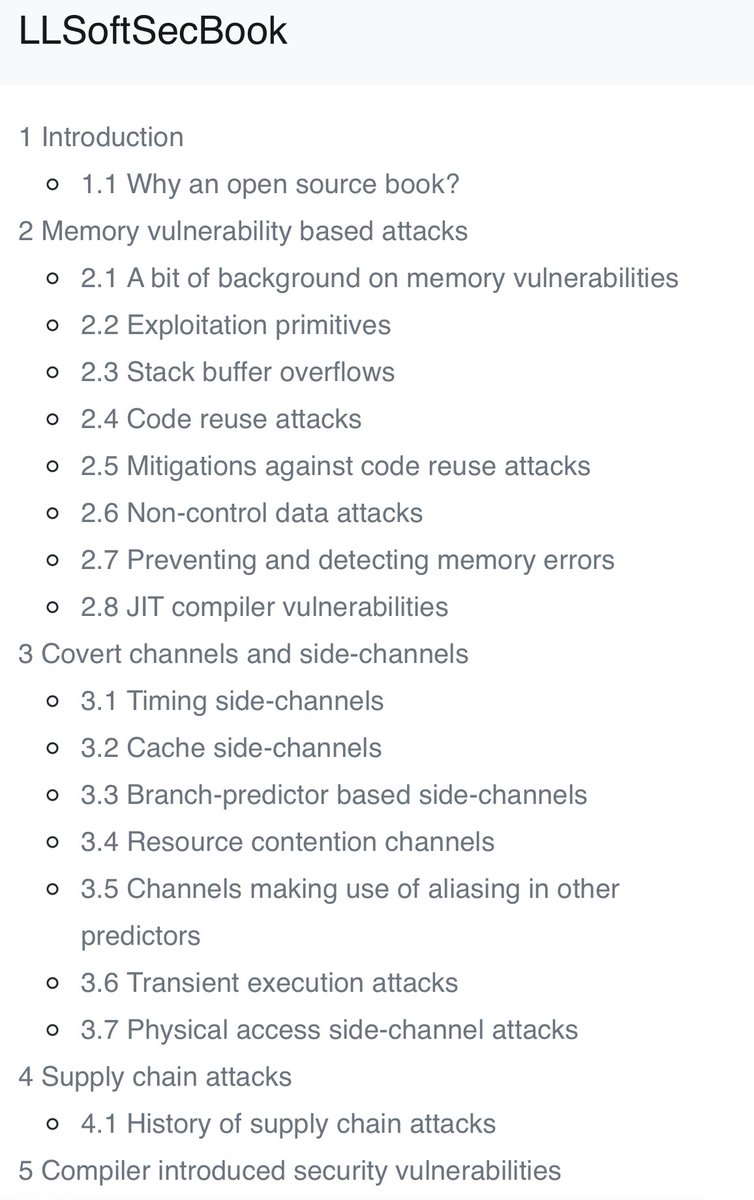
One problem with software security is that there are lots of materials explaining specific vulns or exploits but not many giving a broad structured overview in one place. This free book llsoftsec.github.io/llsoftsecbook/ on Low-Level Security for Compiler Developers aims to address this.
░M░A░L░W░A░R░E░ ░I░N░ ░B░I░O░
After a long time, the 6th and final part of Lord Of The Ring0 is here: idov31.github.io/posts/lord-of-… In this part, the focus will be on kernel mode and user mode memory interaction, look into how attaching process work, and writing an AMSI bypass driver #infosec #CyberSecurity

John Hammond @_JohnHammond
240K Followers 2K Following Hacker. Cybersecurity Researcher @HuntressLabs || https://t.co/qUeDM3lSCl
GuidedHacking @GuidedHacking
37K Followers 329 Following Reverse Engineering, Game Hacking, Malware Analysis & Exploit Development @ https://t.co/Dl5ED4o7YS
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Rad @rad9800
6K Followers 830 Following labs @praetorianlabs opinions are my own and not of my employer
x86matthew @x86matthew
17K Followers 344 Following C / asm / reverse engineering. Developer at @MDSecLabs. Other stuff at @the_secret_club
DebugPrivilege @DebugPrivilege
37K Followers 2K Following Security “Researcher” | Former Microsoft MVP | All Tweets are my opinions and thoughts. Interested in Security, Debugging, and Troubleshooting.
Jiří Vinopal @vinopaljiri
8K Followers 429 Following Threat Researcher at Check Point @_CPResearch_ #DFIR #Reversing - All opinions expressed here are mine only. https://t.co/iWvwWF1AnN
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon) https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
Battle Programmer Yuu @netspooky
18K Followers 1K Following knuck if you buck 日本語/español OK (he/they) @tmpout @binarygolf @[email protected]
klez @KlezVirus
6K Followers 668 Following Principal Cyber Security Consultant at Digital Trust Consulting Services, BSI - Opinions are my own
Kostas @Kostastsale
16K Followers 364 Following @TheDFIRReport member | Tweeting and following mostly #ThreatIntel,#malware,#IR & #Threat_Hunting. Opinions are mine only! 🇬🇷🇨🇦
Adam @Hexacorn
24K Followers 1K Following Red Brain, Blue Fingers [email protected] https://t.co/Bm0C9KQDDY RIP Twitter
Jean @Jean_Maes_1994
11K Followers 1K Following Director of Advanced Assessments -EU @neuvik | @sansoffensive Certified instructor/SEC565 author/SEC699 co author https://t.co/haRI3ruvlg
Matthew @embee_research
12K Followers 1K Following Malware Researcher & Reverse Engineer | Creating and Sharing Educational Cyber Content
Myrtus @Myrtus0x0
7K Followers 699 Following Malware Researcher | Developer | @Cryptolaemus1 | @Proofpoint. Will happily talk about malware with anyone. bsky: [email protected]
Nikhil @Ox4d5a
15K Followers 1K Following Penetration Tester | i XCHG 0's 1's and do hacks | Red Team Sorcery https://t.co/6LUhkvNA77 | #eJPT | #OSCP | #CRTP | #CRTA | #CESP | #CRTE
Janice Westenberger @JaniceWest19113
94 Followers 5K Following
webchick at Aiven �.. @webchick
21K Followers 13K Following Director of Community @aiven_io. Formerly @MongoDB @Drupal. @OReillyMedia author. Lesbionic Ace Mom. #AuDHD? Gendermeh. Gamer. Views my own.
sink0Rswim @laceandload
107 Followers 2K Following
Nitesh Surana @_niteshsurana
325 Followers 657 Following Cloud Security Research w/ @trendmicro | Microsoft MVR | Black Hat USA, Asia Speaker | Prev. Blue Teaming w/ @tcs | TCS HackQuest 3.0 Finalist
Money Dex @MakeMoneyDex
0 Followers 562 Following
RAG intern @_nickhurt
629 Followers 1K Following Looking to replace my car’s extended warranty, RAG judas, hyperstitional cargo-hauler 🎟️
Kyle Cucci @d4rksystem
4K Followers 489 Following Threat Research @proofpoint | Author of "Evasive Malware" @nostarch | Talks about cybercrime, threat intel, and malware stuff.
Victor vdH @D0y0u3v3nl33t
228 Followers 888 Following Red team enthusiast, malware tinkerer and pentester
Safa Punter @punt_sa
15 Followers 3K Following
Jillian Orosco @OrosJillia
35 Followers 5K Following
Lyla Geneseo @lyl_genes
82 Followers 5K Following
Veronika Tejadilla @VeronikaTe29913
74 Followers 5K Following
Chaya Landers @chay_lande
69 Followers 5K Following
Almohaned Albahri @mo_ba7ri
5 Followers 69 Following
Cleo Atteburg @atteburg24551
78 Followers 5K Following
Vivienne Sours @sour_vivie
60 Followers 5K Following
555gstate @555gstate
19 Followers 215 Following
Amit Sahu @ameetsaahu
270 Followers 580 Following Vuln Research | Exp Dev | CTFs with @Water_Paddler
MikeWavada @WavadaMike
214 Followers 3K Following Cyber specialist specializing in Imposter Syndrome. Former USMC. Currently with Prestige Worldwide. Likes Nickelback.
Cracked Enigma @mrm33s33k5
5 Followers 24 Following
rewscel @rewscel
32 Followers 688 Following
hans.h @ghost1nwires
79 Followers 2K Following // Fear of serious injury cannot alone justify suppression of free speech and assembly - Louis, 1927
Tennille Olecki @OlecTennil
77 Followers 5K Following
Lela Husmann @HusmannLel45019
74 Followers 5K Following
Dalton @0ptyxx
21 Followers 84 Following husband | father | software engineer & amateur vulnerability researcher
Matt Zorich @reprise_99
11K Followers 2K Following @Microsoft GHOST 👻 | https://t.co/HWozKuj5IQ | Tweets are my own
Kaylyn Schroeder @SchroederK76920
59 Followers 3K Following
Dinesh_Devadoss @dineshdina04
799 Followers 922 Following Threat Hunter | Malware Analyst | Reverse Engineer | Wanderer in the world of binary
somedieyoungZZ @IdaNotPro
62 Followers 154 Following Threat Hunter | Malware Analysis sudo pacman -S kimsuky
Josh Long (the JoshM.. @theJoshMeister
151K Followers 3K Following Chief Security Analyst; cybersecurity researcher, infosec writer, public speaker, & podcaster. Focused on Apple, Mac, macOS, malware, privacy, & online safety.
4sale_r9057 @here4nauR9057
311 Followers 2K Following Random dude on the net.Using the internet to deprogram myself.Some might say I'm a nut.👁️👂🏾2RKELE Pronouns:I have a dick okay More to come...
McLapse @McLapse30998
206 Followers 3K Following
june @0x5cff3d
1 Followers 75 Following
Abdullah ALmabdi . @ALmabdi
122 Followers 5K Following Computer Network Student, Security OS Linux 🐧❤️🇸🇦💻 @ittihad @fcbayern
Dalton_Ke @Dalton254_ke
705 Followers 727 Following Software Developer | Cloud & Network Analyst #SoftwareDev #Cloud #DevOps
vx-underground @vxunderground
291K Followers 211 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
ςεяβεяμs - м�.. @c3rb3ru5d3d53c
21K Followers 235 Following 💕 Malware Hunter Killer 💕 #binlex & #mwcfg Developer 📽️ YouTuber 👩💻 She/Her 💍@DravenSwiftbow Support my work 👇 ☕️ https://t.co/SfTI8uJa23
GuidedHacking @GuidedHacking
37K Followers 329 Following Reverse Engineering, Game Hacking, Malware Analysis & Exploit Development @ https://t.co/Dl5ED4o7YS
cts🌸 @gf_256
52K Followers 624 Following Co-founder @zellic_io & @pb_ctf | YT: https://t.co/nlNai6iQCn Prev: Vector35, Grayshift, Two Sigma, Dfsec | 23yo hacker femboy
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Rad @rad9800
6K Followers 830 Following labs @praetorianlabs opinions are my own and not of my employer
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
x86matthew @x86matthew
17K Followers 344 Following C / asm / reverse engineering. Developer at @MDSecLabs. Other stuff at @the_secret_club
DebugPrivilege @DebugPrivilege
37K Followers 2K Following Security “Researcher” | Former Microsoft MVP | All Tweets are my opinions and thoughts. Interested in Security, Debugging, and Troubleshooting.
Grzegorz Tworek @0gtweet
29K Followers 1K Following My own research, unless stated otherwise. Not necessarily "safe when taken as directed". GIT d- s+: a+ C++++ !U !L !M w++++$ b++++ G-
Alexandre Borges @ale_sp_brazil
23K Followers 111 Following Vulnerability Researcher and Exploit Developer
Yarden Shafir @yarden_shafir
19K Followers 272 Following A circus artist with a visual studio license
Karsten Hahn @struppigel
22K Followers 702 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Alh4zr3d @Alh4zr3d
19K Followers 283 Following Legal Criminal | Twitch cult leader | InfosecPrep founder | Lovecraft scholar | Soros mercenary | Spiritual cargo shorts wearer | Cthulhu fhtagn
reverseame @reverseame
16K Followers 1 Following RME-DisCo research group from University of Zaragoza. Special interest on software and systems security. Link to our Telegram channel: https://t.co/UmkcXVG8MU
Nitesh Surana @_niteshsurana
325 Followers 657 Following Cloud Security Research w/ @trendmicro | Microsoft MVR | Black Hat USA, Asia Speaker | Prev. Blue Teaming w/ @tcs | TCS HackQuest 3.0 Finalist
SandboxEscaper @big_polar_bear1
2K Followers 281 Following Fan of quadratic residues Former microsoft employee selling windows 0days.
Amit Sahu @ameetsaahu
270 Followers 580 Following Vuln Research | Exp Dev | CTFs with @Water_Paddler
Cracked Enigma @mrm33s33k5
5 Followers 24 Following
Oversecured @OversecuredInc
3K Followers 0 Following Securing the mobile world 🌐 We know how to protect your Android & iOS apps with our robust vulnerability-scanning solutions #MobileAppSecurity #Cybersecurity
hans.h @ghost1nwires
79 Followers 2K Following // Fear of serious injury cannot alone justify suppression of free speech and assembly - Louis, 1927
Ismael Valenzuela @aboutsecurity
17K Followers 9K Following VP Threat Research & Intelligence @BlackBerry ▪️ Ex @Foundstone @Intel @McAfee ▪️ SANS Senior Instructor, GSE #132 ▪️ Author #SEC530 #SEC568 #ThinkRedActBlue
Off-By-One Conference @offbyoneconf
283 Followers 96 Following A premier gathering of offensive cybersecurity professionals, researchers, thought leaders and innovators from around the region.
Cyber Team @Cyberteam008
911 Followers 50 Following Threat Hunting | APT Tracking | Malware Analysis | Darkweb Monitoring "Unity is Strength"
Zero Day Engineering @zerodaytraining
6K Followers 1 Following Vulnerability Research & Courses • https://t.co/WDjQQrzTtR
Matt Zorich @reprise_99
11K Followers 2K Following @Microsoft GHOST 👻 | https://t.co/HWozKuj5IQ | Tweets are my own
Kijo Ninja @kj_ninja25
2K Followers 87 Following Security Engineer @Microsoft - EDR, XDR, KQL, ThreatHunting | #Triathlete 🏊♂️ 🚴 🏃♀️ National Team (Age group).. or KJ Ninja 🥷 My tweets are my own
Manfred Paul @_manfp
5K Followers 279 Following Maths and cyber and stuff. Playing CTFs with @redrocket_ctf (and @Sauercl0ud). Pwn2Own Vancouver 2020..=2022, 2024. @[email protected]
Zero Day Initiative @thezdi
77K Followers 17 Following Trend Micro’s Zero Day Initiative (ZDI) is a program designed to reward security researchers for responsibly disclosing vulnerabilities.
Intel-Ops @Intel_Ops_io
2K Followers 4 Following Adversary Infrastructure Hunting & Training Curated Threat Intelligence Feed (Coming Soon) https://t.co/N9OKrTrvV0 https://t.co/3YFZfEbgpI
simo @_simo36
7K Followers 107 Following
RussianPanda 🐼 �.. @RussianPanda9xx
8K Followers 350 Following Senior Threat Intelligence Researcher at @esthreat | Threat Hunter | Malware Addict
Women CyberSecurity S.. @WomenCSSociety
13K Followers 9K Following ❤️🇨🇦 Award winning non-profit🔆supporting 💟women in 🚺 cybersecurity 💻 @womenincyberday #EmpoweringWomenForCyber™️! #IWCD™️ #TippingTheScale™️ ⚖️❤️
Josh Long (the JoshM.. @theJoshMeister
151K Followers 3K Following Chief Security Analyst; cybersecurity researcher, infosec writer, public speaker, & podcaster. Focused on Apple, Mac, macOS, malware, privacy, & online safety.
Matthew @embee_research
12K Followers 1K Following Malware Researcher & Reverse Engineer | Creating and Sharing Educational Cyber Content
安坂星海 Azaka �.. @AzakaSekai_
9K Followers 1K Following 台湾 / Taiwan (中/En) - 🖌️ #artsyaz Comfy VTuber / threat intelligence researcher (NOT independent) Model + rig @jamama_666 // add. rig @justNovaj
TyphoonCon🌪️ @typhooncon
6K Followers 4 Following TyphoonCon is an annual all Offensive Security Conference, taking place May 27-31, 2024 in Seoul, South Korea. Tickets are now on sale! 🌪️
Gabriel Landau @GabrielLandau
3K Followers 701 Following WinDbg’er @ Elastic Security. Thoughts are my own. Some of my writing: https://t.co/EMJxj12lut More: https://t.co/pxG2OnO1OC @[email protected]
Boris Larin @oct0xor
17K Followers 518 Following Former console hacker (PS3/PS4). Hunting in the wild 0-days at Kaspersky GReAT. All tweets are my own.
Michal Strehovský @MStrehovsky
7K Followers 176 Following I help building the .NET runtime at Microsoft. My tweets are my own opinions and/or shitposts, not the official party line.
bot59751939 👽🏴�.. @bot59751939
303 Followers 322 Following I created and run @vxunderground 's Black Mass zine. Process virtual machine enthusiast. | PTC
Dodo on Security 🇵.. @dodo_sec
2K Followers 875 Following Brazilian Security Analyst | Malware Analysis | Responsible for the Slowest Algo in HashDB | Can barely reverse Hello World | PTC
Josh @passthehashbrwn
7K Followers 344 Following Adversarial Simulation at IBM, tweets are mine etc.
Gal Z @0xgalz
7K Followers 427 Following Security Researcher. Reverse Engineering 💙 Vulnerability Research 💜 Embedded 🤖 C++🤩 OS Internals 🤍 Sewing🧵 Classical Music🎼 Opinions are my own.
Alexa Souza @w4fz5uck5
558 Followers 144 Following Co-Founder & CTO at ViperX | Speaker at H2HC & BHACK | OSCP¹⁸ʸ | OSCE¹⁹ʸ | OSWE²¹ʸ | 🏳️⚧️
Ido Veltzman @Idov31
3K Followers 37 Following I'm a security researcher that using this platform to share my projects and research. Opinions are my own. https://t.co/UiWgKq40sV
Alex Matrosov @matrosov
18K Followers 2K Following 🔬Founder & CEO @Binarly_io, #codeXplorer, #efiXplorer, @REhints and "Rootkits and Bootkits" book. Previously worked at Nvidia, Cylance, Intel, ESET, Yandex.
ThreatBook @ThreatBookLabs
3K Followers 23 Following Expert on cyber threats detection and response. Fast detect and respond to threats with high-fidelity, efficient, actionable security intelligence.
Images That Could Be .. @ImagesAlbum
2.0M Followers 79 Following Digital artist and photographer. I create album covers. DM for enquiries.
naridarbandi @naridarbandi
12K Followers 2K Following Full Time Visual Artist/photographer/ [email protected]/ NFT/PRINT/COVER MUSIC/ https://t.co/MPac5p74Yh
Binary Golf Associati.. @binarygolf
1K Followers 39 Following Binary Golf Grand Prix ; Annual Small File Competition ; Less Is More ; #BGGP4 begins June 23th 2023, ends August 25th 2023
Dagmawi Mulugeta @dagmulu
131 Followers 567 Following Talk security to me. Here are my Grammarly approved thoughts while I wait to become educated ;) Tweets are my own
Cat @coolestcatiknow
2K Followers 319 Following Infosec-er, nerd, artist and vet. Work @mitreattack as a leader and contributor. 💖🍎🐧👩💻. Opinions are like 🐰🕳, they change the more you know.
Anshu 🕸️ @thebitdoodler
4K Followers 185 Following Security Research @CloudSEK && Simplifying Security Concepts @ https://t.co/jCpnCaAwER • Views are Personal
Outflank @OutflankNL
5K Followers 11 Following Offensive Tooling for Red Teams, Red Teaming and Trainings
Abhinav Pandey @Abhinavvpandeyy
287 Followers 416 Following Cyber Threat Researcher @cloudsek | Founder @Cyv3rsity | HackerDifficult vulnerabilities make you more cultured. Difficult exploits make you more persistent. Difficult detection evasion makes you wiser. If in doubt, choose the more difficult path.
I have a new offensive security blog and a malware development series called Flying Under the Radar. Let me know your thoughts. Part 1 is about Resolving Sensitive Windows Functions with x64 Assembly: theepicpowner.gitlab.io/posts/Flying-U… Introduction to the series: theepicpowner.gitlab.io/posts/Flying-U…
Released a new version of OleViewDotNet (v1.14) on the PS gallery. A big change is better source code formatting for proxies and typelibs in IDL format rather than the old pseudo C# one. The video below also shows an example of dynamic parsing and display of source in the UI.
Systematic browser vulnerability research is a next level productivity challenge. This Notion of mine is a small fraction of it with only JavaScript Engines, mostly v8, recent, and actual analysis output not shown! 🥵
Microsoft has identified longstanding activity by the Russian-based threat actor we track as Forest Blizzard using a custom tool we call GooseEgg to exploit CVE-2022-38028 in the Windows Print Spooler service to elevate permissions and steal credentials: msft.it/6014YG3oI
We are approaching 300,000 followers on Twitter. This is an astronomically large number that we never expected to reach. Some thoughts and feelings: When vx-underground was first created in May, 2019 the initial goal was to 'revive the VX-scene' – with the hopes that with…
NOW LEAVE ME ALONE, YOU PACK OF ABSOLUTE GOBLINS
Google Dork - Sensitive Docs 📄 ext:txt | ext:pdf | ext:xml | ext:xls | ext:xlsx | ext:ppt | ext:pptx | ext:doc | ext:docx intext:“confidential” | intext:“Not for Public Release” | intext:”internal use only” | intext:“do not distribute” Discover internal files 👀
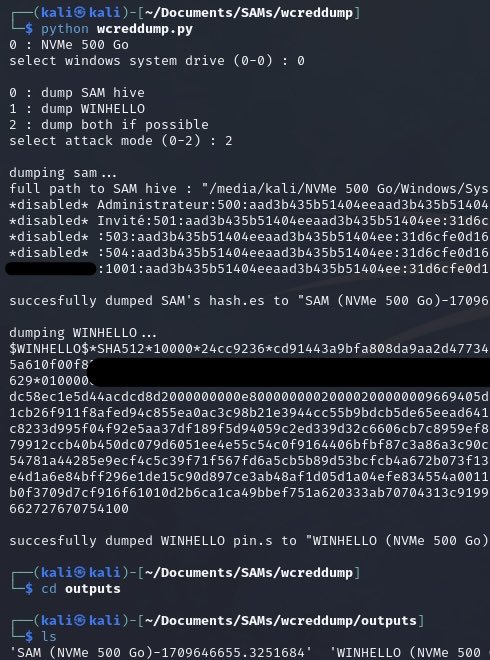
Did you know that LSASS has the ability to execute arbitrary kernel-mode addresses? I wrote a small proof of concept that allows administrators to execute unsigned code in the kernel if LSA Protection is disabled. github.com/floesen/KExecDD
Bye bye to my admin->kernel priv8 0day 👋 Was sitting on it due to an NDA and i thought it was a quite unique bug, turns out it wasn't. TTP burned 🔥 I might have a blogpost in the future in which i describe how i (differently) exploited it, let's see if time permits...
Did you know that LSASS has the ability to execute arbitrary kernel-mode addresses? I wrote a small proof of concept that allows administrators to execute unsigned code in the kernel if LSA Protection is disabled. github.com/floesen/KExecDD
A GitHub flaw lets attackers upload executables that appear to be hosted on a company's official repo, such as Microsoft's—without the repo owner knowing anything about it. The following URLs, for example, make it seem like these ZIPs are present on Microsoft's source code repo:…
I’ve been quite silent lately, very busy with Magika: my knowledge of file formats increased tenfold at least. I long stopped counting how many specs, corpus or parsers I’ve explored recently. “File format X: yet another mess”
CVE-2024-21338:Windows Kernel Elevation of Privilege Vulnerability CVE-2024-21338 patch. The vulnerability occurs at certain IOCTL of “appid.sys”... This exploit targets appid.sys driver and works for both Windows 10 & 11 with HVCI enabled. PoC github.com/Nero22k/Exploi…